database-firewall0 pages
ORACLE DATA SHEET
ORACLE DATABASE FIREWALL
A POWERFUL, SCALABLE,
ENTERPRISE DATABASE FIREWALL
KEY FEATURES
Flexible deployment models
include monitoring, and blocking
White list, black list, and exception
list based policies
Highly scalable architecture for
enterprise applications
Dozens of built-in customizable
compliance reports
Real-time security alerts
Supports Oracle, MySQL,
Microsoft SQL Server, Sybase,
and IBM DB2
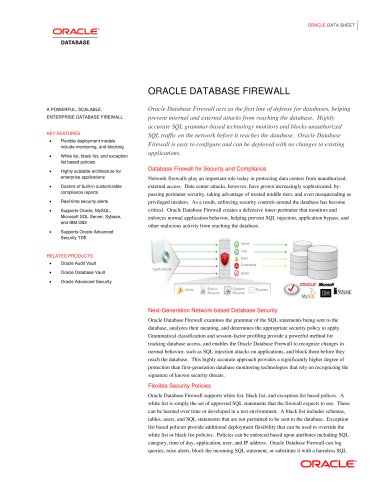
Oracle Database Firewall acts as the first line of defense for databases, helping
prevent internal and external attacks from reaching the database. Highly
accurate SQL grammar-based technology monitors and blocks unauthorized
SQL traffic on the network before it reaches the database. Oracle Database
Firewall is easy to configure and can be deployed with no changes to existing
applications.
Supports Oracle Advanced
Security TDE
Database Firewall for Security and Compliance
Network firewalls play an important role today in protecting data centers from unauthorized,
external access. Data center attacks, however, have grown increasingly sophisticated, bypassing perimeter security, taking advantage of trusted middle tiers, and even masquerading as
privileged insiders. As a result, enforcing security controls around the database has become
critical. Oracle Database Firewall creates a defensive inner-perimeter that monitors and
enforces normal application behavior, helping prevent SQL injection, application bypass, and
other malicious activity from reaching the database.
RELATED PRODUCTS
Oracle Audit Vault
Oracle Database Vault
Oracle Advanced Security
Next-Generation Network-based Database Security
Oracle Database Firewall examines the grammar of the SQL statements being sent to the
database, analyzes their meaning, and determines the appropriate security policy to apply.
Grammatical classification and session-factor profiling provide a powerful method for
tracking database access, and enables the Oracle Database Firewall to recognize changes in
normal behavior, such as SQL injection attacks on applications, and block them before they
reach the database. This highly accurate approach provides a significantly higher degree of
protection than first-generation database monitoring technologies that rely on recognizing the
signature of known security threats.
Flexible Security Policies
Oracle Database Firewall supports white list, black list, and exception list based polices. A
white list is simply the set of approved SQL statements that the firewall expects to see. These
can be learned over time or developed in a test environment. A black list includes schemas,
tables, users, and SQL statements that are not permitted to be sent to the database. Exception
list based policies provide additional deployment flexibility that can be used to override the
white list or black list policies. Policies can be enforced based upon attributes including SQL
category, time of day, application, user, and IP address. Oracle Database Firewall can log
queries, raise alerts, block the incoming SQL statement, or substitute it with a harmless SQL

 عضویت
عضویت  ورود اعضا
ورود اعضا راهنمای خرید
راهنمای خرید