SSG5 and SSG20 Secure Services Gateways0 pages
DATASHEET
SSG5 AND SSG20
SECURE SERVICES
GATEWAYS
Product Overview
The Juniper Networks SSG5 and
SSG20 Secure Services Gateways
are purpose-built security appliances
that deliver a perfect blend of
performance, security, routing and
LAN/WAN connectivity for small
branch offices, fixed telecommuters
and small standalone business
deployments. Traffic flowing in and
out of the branch office or business
is protected from worms, spyware,
trojans, and malware by a complete
set of Unified Threat Management
security features that include
stateful firewall, IPsec VPN, intrusion
prevention system (IPS), antivirus
(includes antispyware, anti-adware,
antiphishing), antispam and Web
filtering.
Product Description
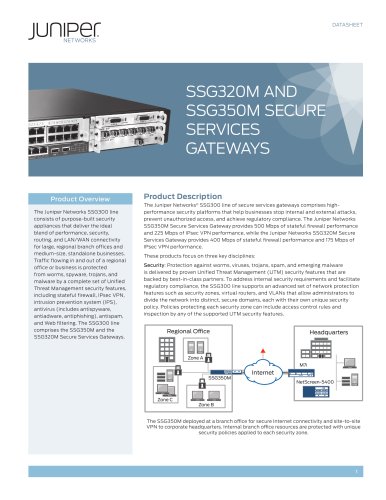
The Juniper Networks® SSG5 and SSG20 Secure Services Gateways are high-performance
security platforms for small branch office and standalone businesses that want to
stop internal and external attacks, prevent unauthorized access and achieve regulatory
compliance. Both the SSG5 and SSG20 deliver 160 Mbps of stateful firewall traffic and
40 Mbps of IPsec VPN traffic.
Security: Protection against worms, viruses, trojans, spam, and emerging malware
is delivered by proven unified threat management (UTM) security features that are
backed by best-in-class partners. To address internal security requirements and
facilitate regulatory compliance, the SSG5 and SSG20 both support an advanced set of
network protection features such as security zones, virtual routers and VLANs that allow
administrators to divide the network into distinct secure domains, each with its own
unique security policy. Policies protecting each security zone can include access control
rules and inspection by any of the supported UTM security features.
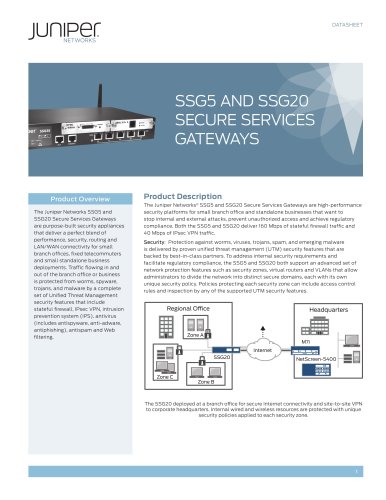
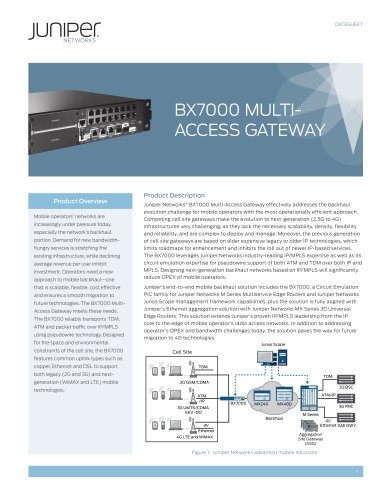
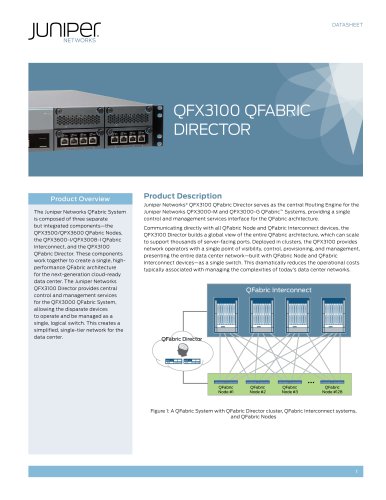
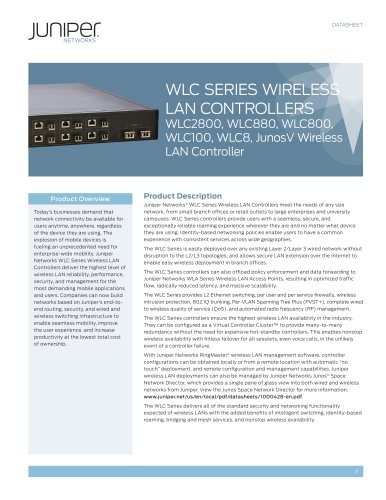
Regional Office
Headquarters
Zone A
M7i
Internet
SSG20
Zone C
NetScreen-5400
Zone B
The SSG20 deployed at a branch office for secure Internet connectivity and site-to-site VPN
to corporate headquarters. Internal wired and wireless resources are protected with unique
security policies applied to each security zone.
1

 عضویت
عضویت  ورود اعضا
ورود اعضا راهنمای خرید
راهنمای خرید